

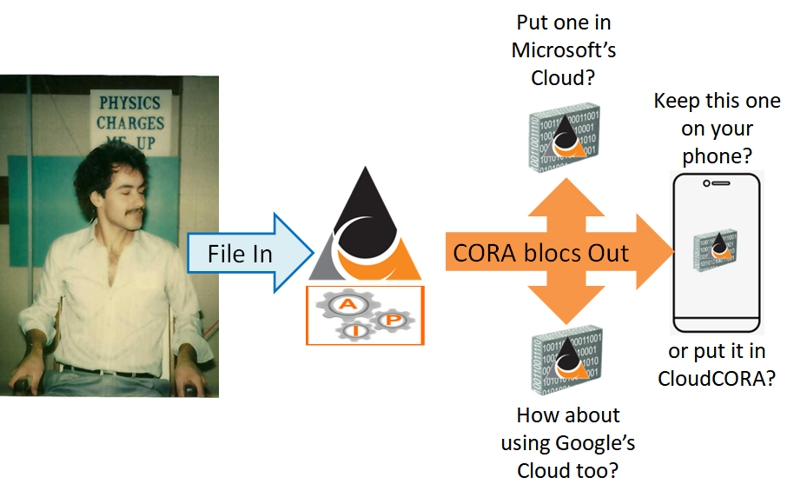
It doesn't matter if they have downloaded it (the CORA bloc), backed it up (the CORA bloc) or emailed it to 1000 goCORA users, no one will ever be able to unCORAfy (decrypt) this picture again!
goCORA provides privacy, data security and cloud security with quantum safe cryptography that is unbreakable. Use goCORA to protect your social media posts, communications and data using CORA for your encryption. Our Multiple Use Pads (MUP) are unlimited in size. Control your online, digital footprint! Delete a single CORA bloc and your communication or post is gone forever.